Securely Build and Deploy Intelligent Azure AI Applications by Integrating Azure Key Vault for Credential and Secret Management
When you create apps that use Azure AI Services (like language or vision APIs), they need keys and endpoints to connect. These are sensitive and should not be hardcoded into your app.
✅ Instead of hardcoding, you can:
- Use Azure Key Vault to store your keys and secrets safely, and let your app retrieve them at runtime.
✅ How It Works:
- You store your Azure AI key and endpoint in Key Vault
- Your app authenticates securely (using DefaultAzureCredential).
- It retrieves the key from Key Vault at runtime.
- Then it uses that key to call Azure AI services.
✅ Why Use Azure Key Vault?
- Protects secrets like API keys, passwords, and endpoints.
- Controls access using Microsoft Entra ID (Azure AD).
- Keeps your app more secure and compliant.
Architecture diagram

Task Details
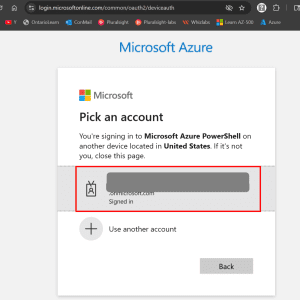
1. Sign in to the Azure Portal
Go to portal.azure.com and log in with your Azure credentials.
2. Create an Azure AI Services Resource
Search for and deploy an Azure AI service (e.g., Language service) in your desired region.
3. Create an Azure Key Vault
Set up a Key Vault to securely store your AI service credentials.
4. Add Secrets to Key Vault
Manually add your AI service key and endpoint as secrets (e.g., AIServiceKey, AIServiceEndpoint).
5. Configure Access Policy
Grant your identity (user or app) permission to read secrets from the Key Vault.
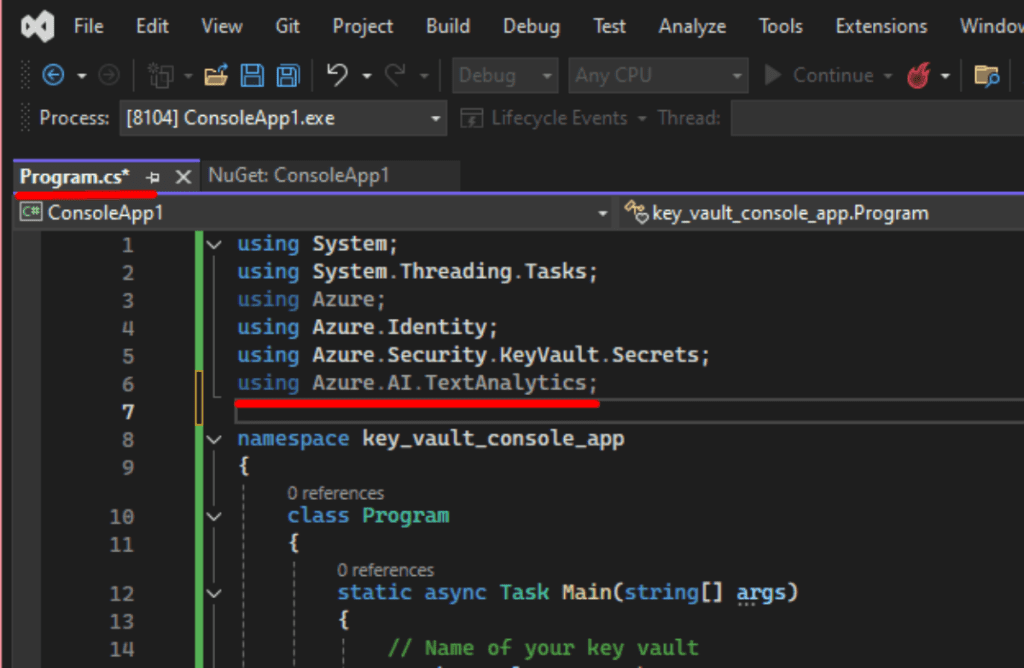
6. Create a C# Console App in Visual Studio
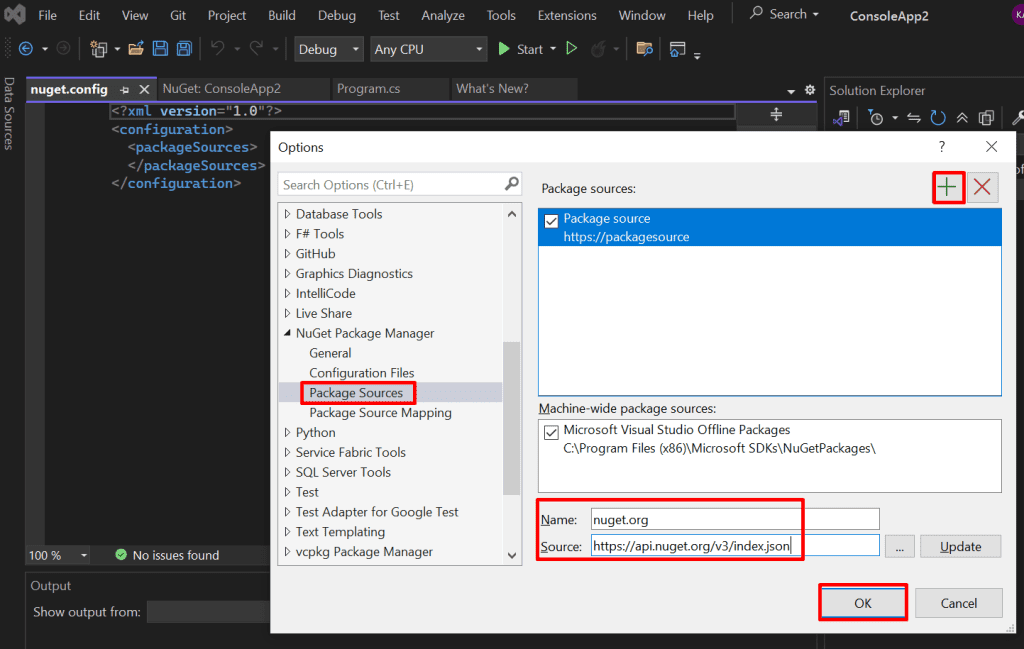
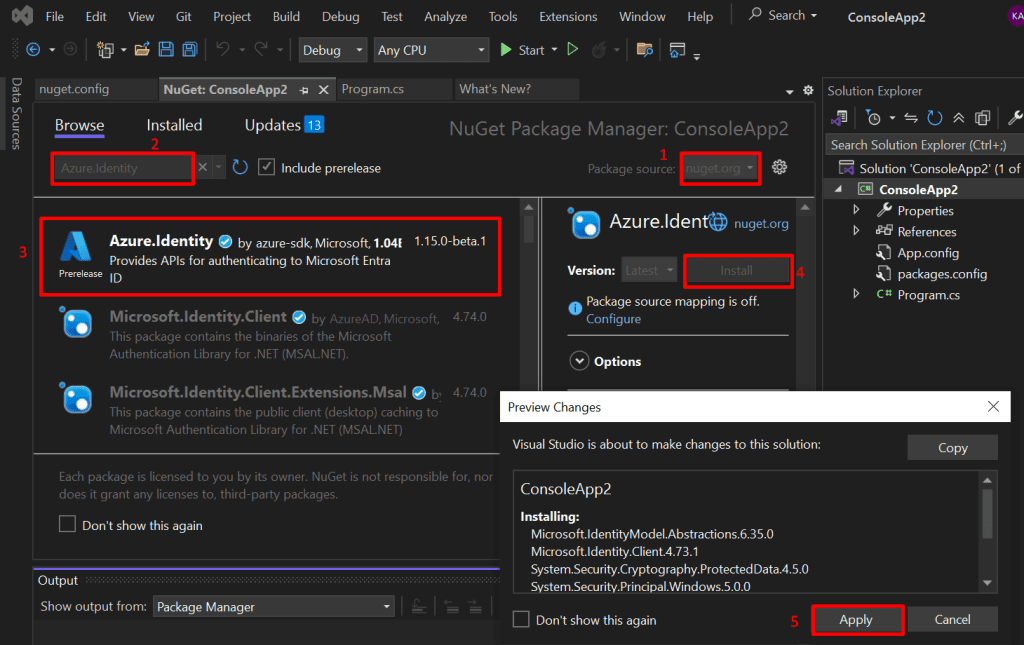
Start a new .NET console project and install the required Azure SDK packages.
7. Call the Azure Language Service
Use the Key Vault secrets to authenticate and send a test request (like NER).
8. Verify the Output
Ensure your app retrieves secrets correctly and returns valid AI results.
*
Steps
1. Create an Azure AI services account.
- In the Azure portal's search bar, type "ai foundry".
- From the search results under "Services," click "Azure AI Foundry."
Note: AI Foundry is used to quickly and securely create AI service accounts with pre-configured settings, automation, and compliance—making setup easier and consistent across projects or teams.

*
2. In the Classic AI Services section, select Azure AI Services (multi-service account), then choose Create Azure AI Services (multi-service account).

*
3. Create Azure AI services with the following details, then "Review + create".
Project Details:
- Select your "Subscription" (e.g., PA).
- Choose an existing "Resource group" (e.g., rg_eastus) or "Create new".
Instance Details:
- Select a "Region" (e.g., "East US").
- Enter a "Name" for your account (e.g., AIaccount).
- Select a "Pricing tier" (e.g., "Standard S0").
Check the box to acknowledge the terms.
Click the "Review + create" button to proceed with deployment.

*
4. Navigate to your newly created Azure AI Services (multi-service) resource, then copy the key and endpoint for later use.

Service Key: 6u8UG271eqqSHzvL6aGXSRhjobUOgOFwTtItAKK8QZDgX9QdS9CGJQQJ99BGACYeBjFXJ3w3AAAEACOGIb7E
Service endpoint value: https://aiaccount.cognitiveservices.azure.com/
*
5. Create an Azure Key Vault.
- In the Azure portal's search bar, type "key" (or "key vaults").
- From the search results under "Services," click "Key vaults."

*
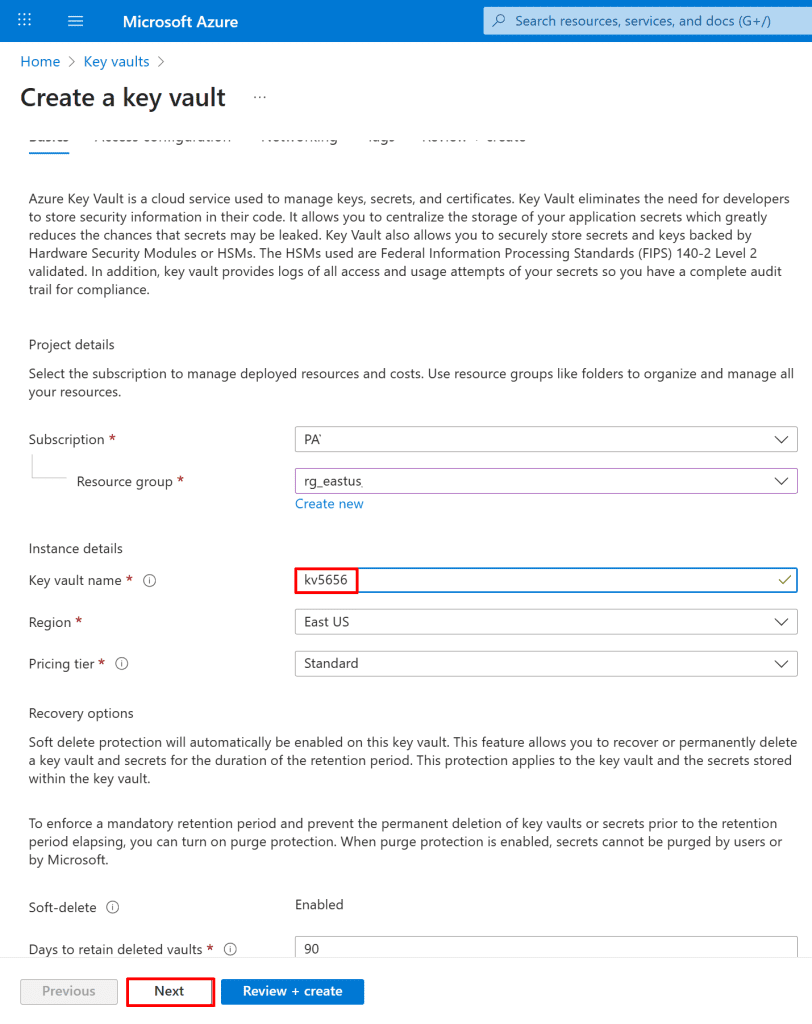
6. Select the following values in the Basics tab, then click next.
Project details:
- Select your "Subscription" (e.g., PA).
- Choose an existing "Resource group" (e.g., rg_eastus) or click "Create new".
Instance details:
- Enter a "Key vault name" (e.g., kv5656).
- Select a "Region" (e.g., "East US").
- Choose a "Pricing tier" (e.g., "Standard").
Click Next: Click the "Next" button to proceed.
*
7. On the Access configuration tab, select vault access policy as the permission model and your current user, then "Review + create" and go to resources.
Note: You can also choose "Azure role-based access control" and then assign your user the Key Vault Crypto Officer role, which is responsible for managing cryptographic keys but not secrets or certificates, or the Key Vault Secrets Officer role, which can manage secrets but not keys, or the Key Vault Administrator role, which can fully manage keys, secrets, certificates, and access policies.

*
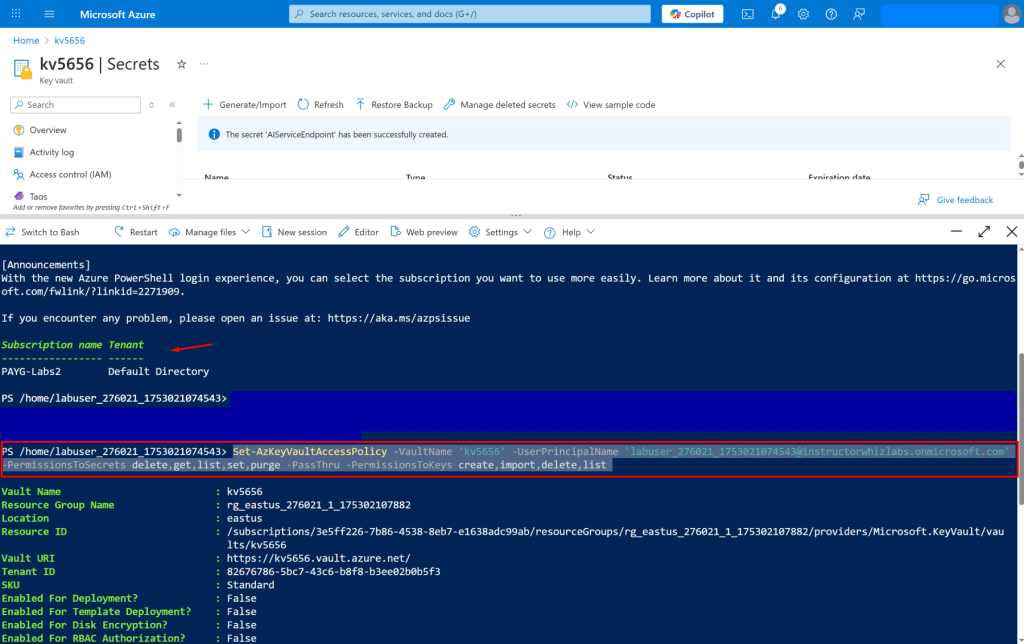
8. In your Azure Key Vault, create two secrets. One for the Azure AI service key and one for the endpoint URL.
- In your Azure Key Vault (e.g., kv5656), click "Secrets" under "Objects" in the left-hand menu.
- Click the "+ Generate/Import" button

*
9. On the "Create a secret" screen in Key Vault, configure the following:
- Upload options: Select Manual
- Name: Enter AIServiceKey
- Secret value: Paste the key you copied from your Azure AI Services resource
- Other settings: Leave all defaults unchanged
Click Create to save the secret.

*
10. On the "Create a secret" screen in Key Vault, configure the following:
- Upload options: Select Manual
- Name: Enter AIServiceEndpoint
- Secret value: Paste the endpoint URL you copied earlier from your Azure AI Services resource
- Other settings: Leave all defaults unchanged
Click Create to save the secret.

*
11. You should now have two secrets created in your Key Vault:
AIServiceKey - contains your Azure AI service API key
AIServiceEndpoint - contains your Azure AI service endpoint URL

*
12. Create an access policy for your Key Vault using Azure PowerShell or CLI to allow your application or user to read secrets.
- Click the Cloud Shell icon (square with _> symbol) in the top right of the Azure portal.
- In the "Welcome to Azure Cloud Shell" prompt, click "PowerShell".
Note:
- Azure PowerShell runs in PowerShell
- Azure CLI can run in Bash, CMD, or PowerShell.
So the distinction is about the tool, not just the shell.

*
13. Select "Mount your storage account", then select the appropriate subscription, and click Apply to proceed.