Configure PIM to assign a User Administrator role, set up a Log Analytics workspace, enable PIM audit logs, integrate Monitor and Entra ID logs, and verify them in Log Analytics.
Task Details
In this project, we’ll configure PIM to assign the User Administrator role with approval, set up a Log Analytics workspace, and enable PIM audit logging. We’ll then integrate Azure Monitor and Entra ID logs to achieve centralized monitoring and enhanced visibility of privileged role activities.
1. Assign user a User Administrator role using Privileged Identity Management (PIM).
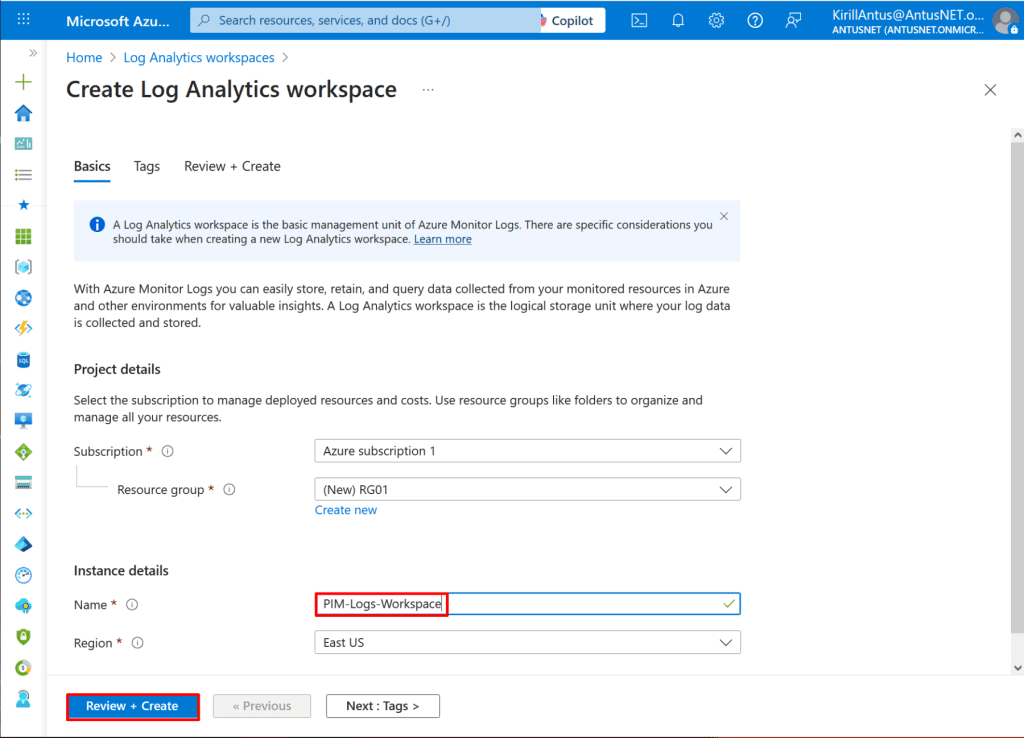
2. Create a Log Analytics Workspace.
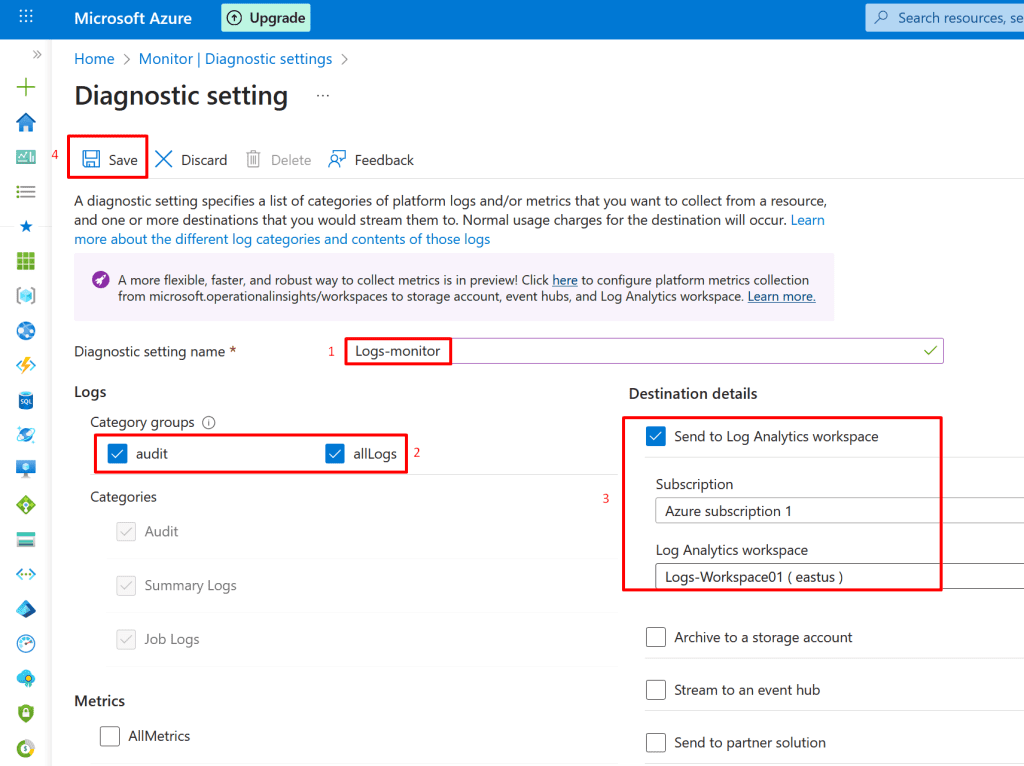
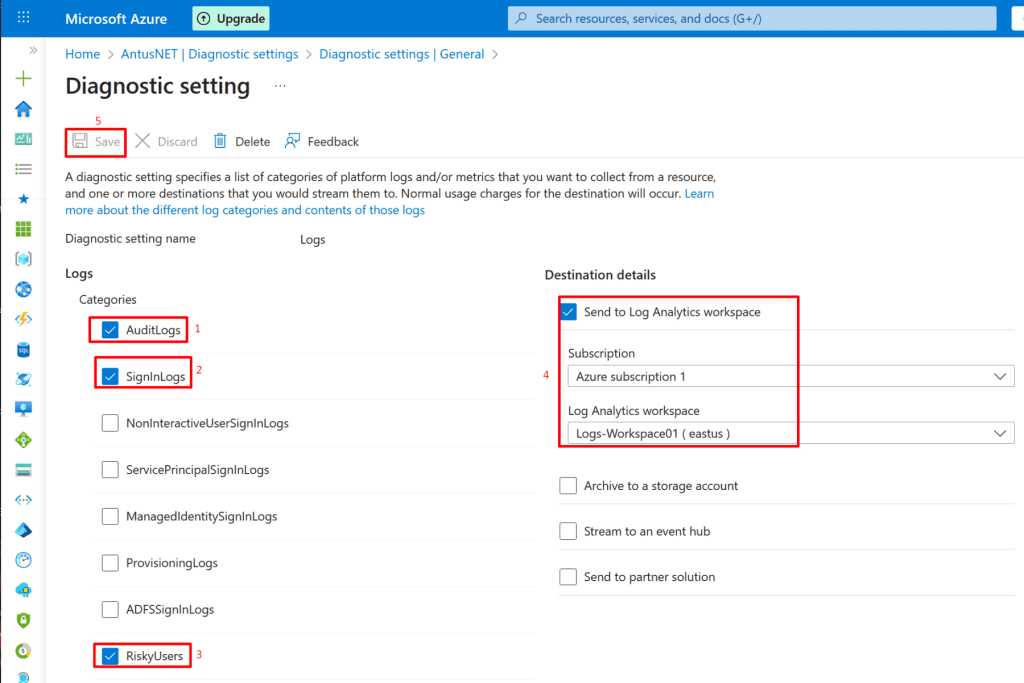
3. Enable PIM Audit Logs.
4. Integrating Monitor Logs and Entra ID Azure to Logs Analytics.
5. Verify logs in Log Analytics.
*
Steps
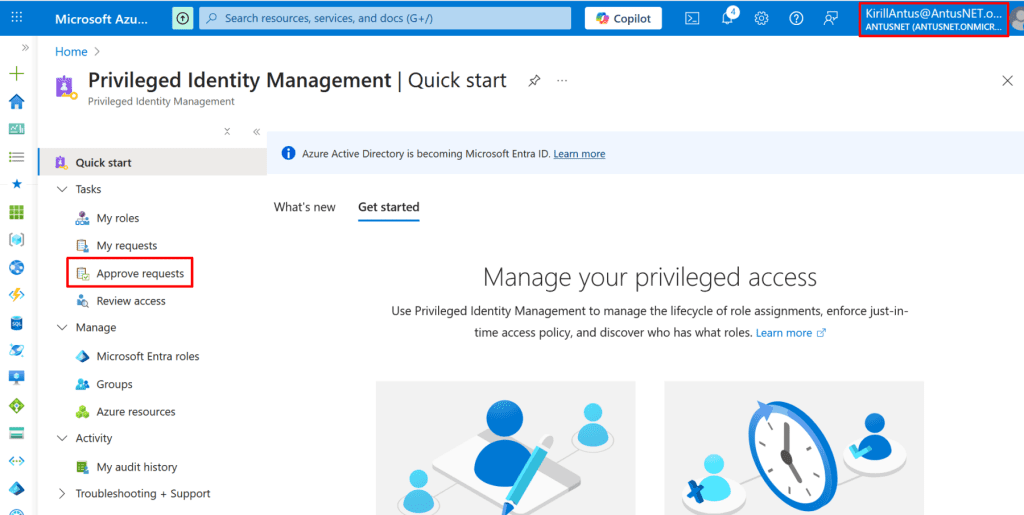
Assign the user a User Administrator role using Privileged Identity Management (PIM).
1. In the search box, type "Privileged Identity Management" and select it.

2. In Privileged Identity Management (PIM), navigate to the Microsoft Entra Roles blade. This section allows you to view, manage, and assign privileged roles, enabling just-in-time access and enforcing least-privilege principles for your users.

3. Select Assign Eligibility to begin configuring which users are eligible for a privileged role. This allows you to define who can activate the role when needed, following the just-in-time access principle.

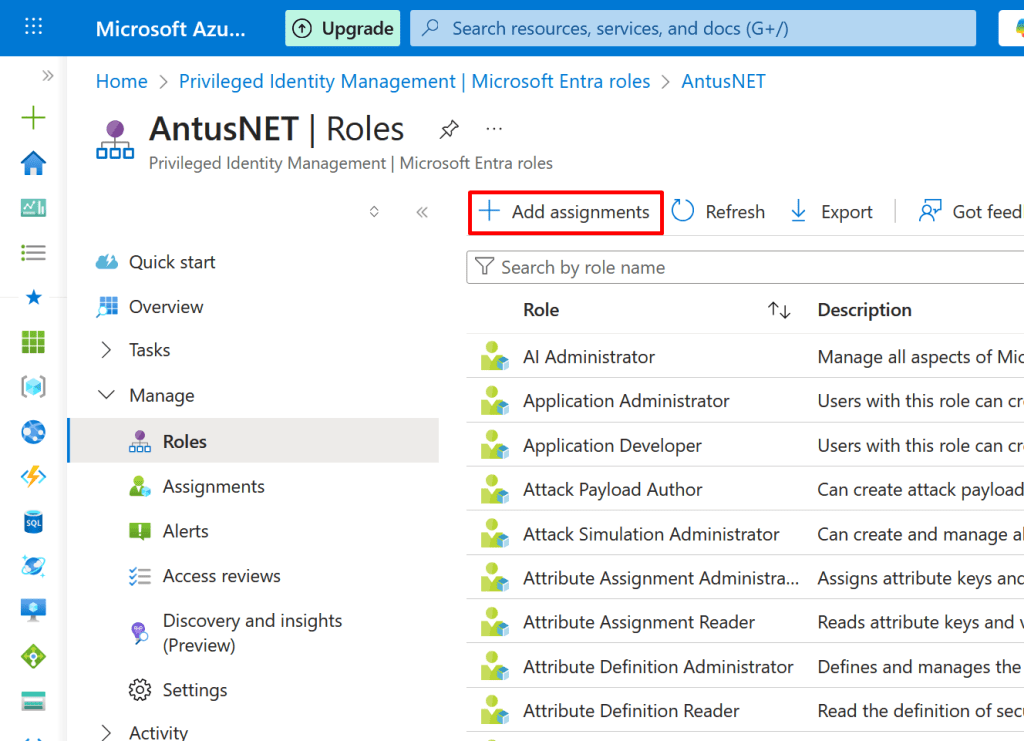
4. Here we can see all the roles available in our environment.
Click Add Assignments to assign the selected user to the User Administrator role.
5. In the Add Assignments blade, choose the role you want to assign and then select the member (user) to receive the role.
- Select User Administrator role
- Select the user to assign the role to.
- Click Select
- Click Next
Note: The selected user has not been assigned any roles yet.


6. Select Eligible to allow the user to activate the role when needed, rather than having permanent access.
- Eligible: The user can activate the role when needed through PIM, supporting just-in-time access.
- Active: This type of assignment is outside of PIM; the user has the role permanently active without requiring activation.
Note:
- Permanent: The user always has the role active.
- Eligible (Time-Based): User must activate the role when needed; access is temporary.
Note: Prefer Eligible in PIM to reduce standing privileges and enhance security.

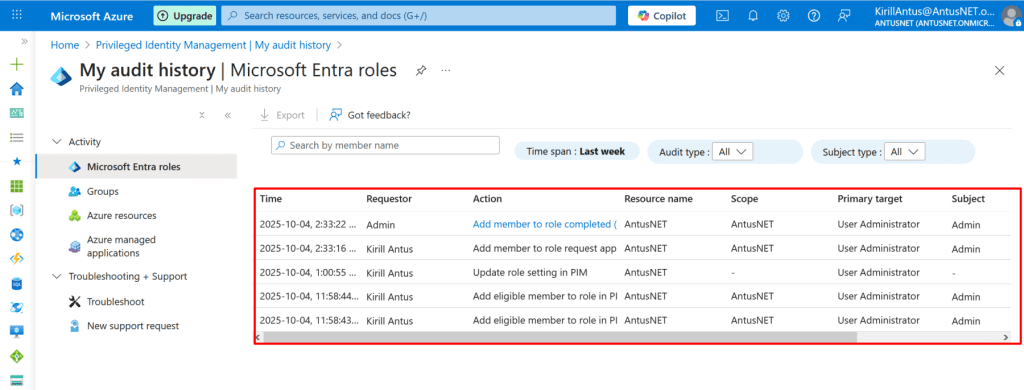
7. In the PIM Assignments blade, you can view all roles currently assigned to the selected user.

8. In the PIM Assignments blade, click on Settings to configure role activation and management options.

9. In the Settings section, click the User Administrator role to configure its settings.

10. In the Role settings details, click Edit to modify the configuration.

11. In the Edit Role Settings page, keep the default settings and check Require approval to activate to ensure activation requires manager approval.
- Select the approver
- Click Next: Assignment
Note: Activation Maximum Duration (hours): The maximum time a user can keep an activated role before it automatically expires. It limits how long elevated access is granted for security purposes.

12. On the Assignments page, set the duration for which a user will remain eligible to activate the role, then click Next: Notification. (In this demo we will use default)

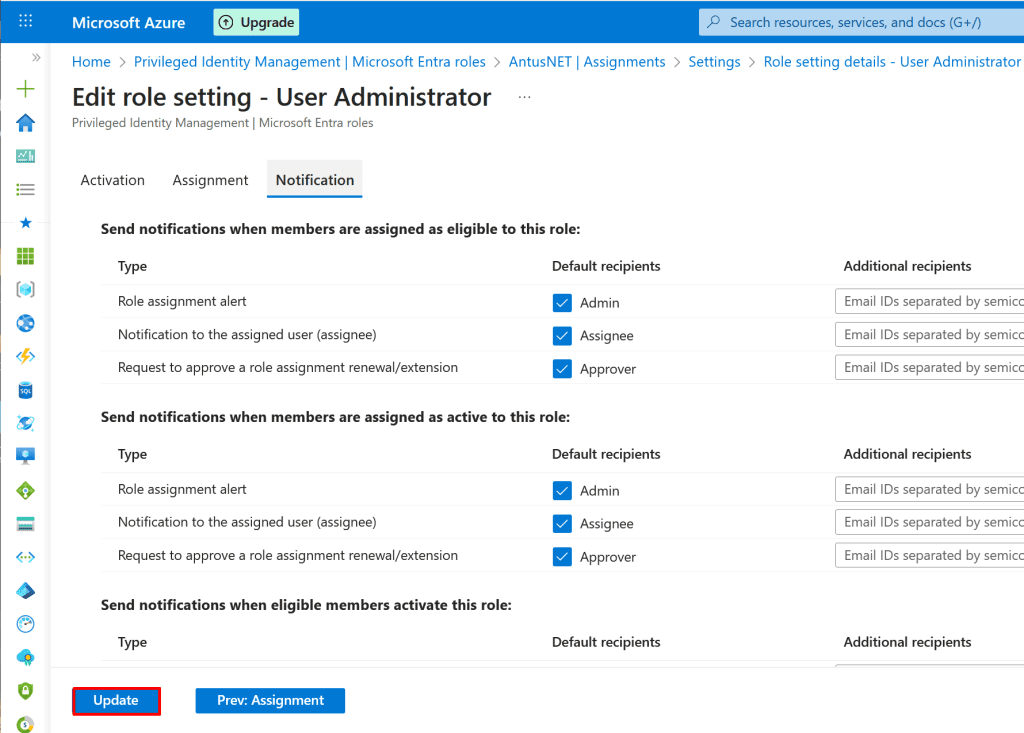
13. On the Notifications blade, keep the default settings and click Update
Note: Notifications Blade (PIM): Displays and configures alerts related to role activation, approvals, and expirations, helping administrators stay informed about privileged access events.
14. Log in as the user to whom you assigned the PIM role. (use private window)
- In the search bar enter PIM
- Select PIM