Deploy Microsoft Sentinel with a Log Analytics workspace, connect VMs via AMA, enable detections and playbooks (including an RDP brute-force email notification), simulate an RDP attack, query logs for detection, automate PowerShell command detection, deploy PowerShell logging to all VMs, and optionally use a GitHub playbook to block an Entra ID user..
Task Details
1. Create Azure Sentinel and Logs analytics workspace.
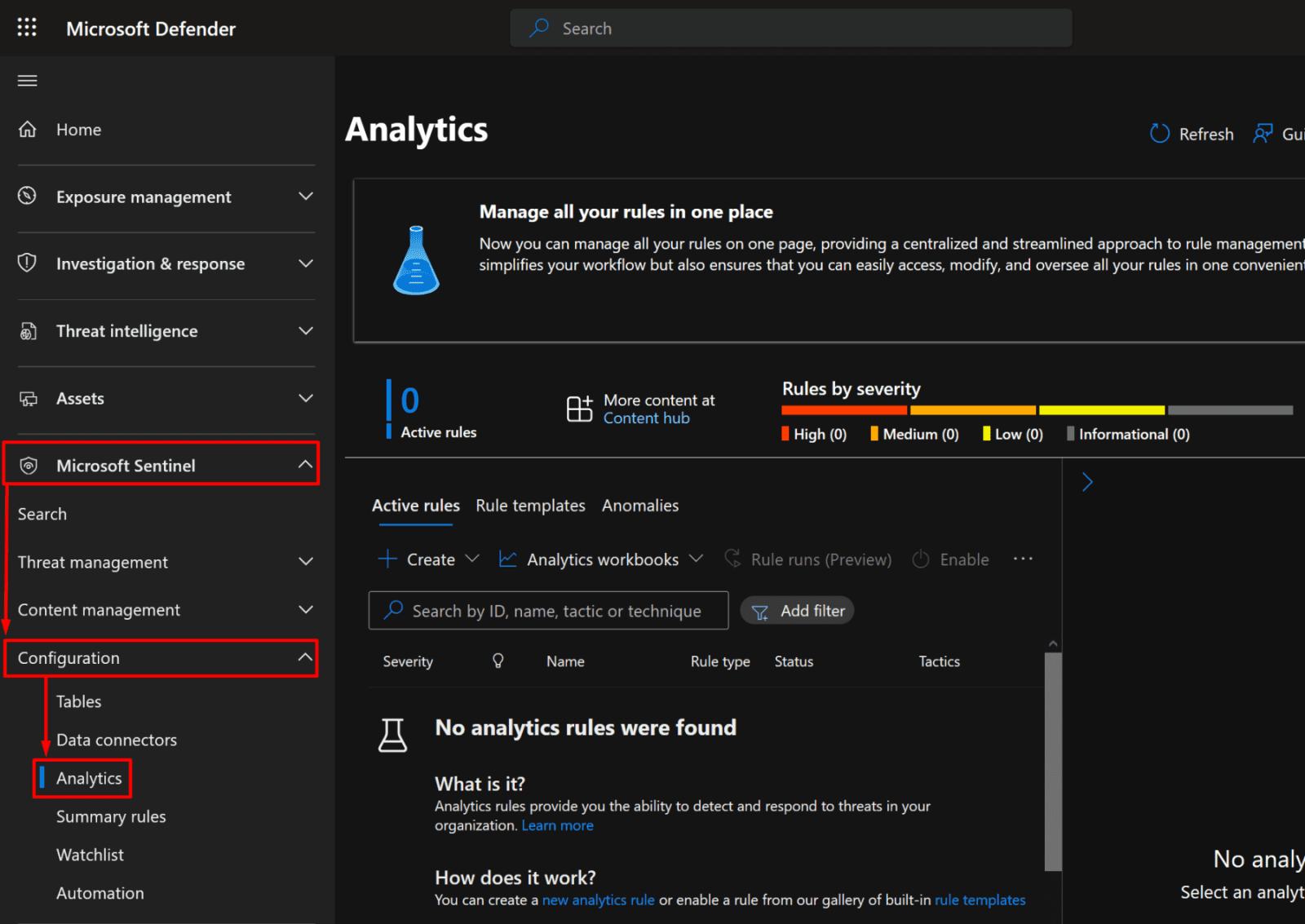
2. Connect Virtual machine to logs analytics workspace using AMA connector in Sentinel portal.
3. Configure prebuilt Analytics rules in sentinel.
4. Create a playbook that automatically emails the administrator when an RDP brute-force is detected.
5. Simulate RDP brute force attack.
6. Query failed login events in the Log Analytics workspace to detect potential RDP brute-force attacks.
7. Automate response using a scheduled query rule to detect PowerShell command execution.
8. Deploy automated PowerShell logging on all VMs in the subscription.
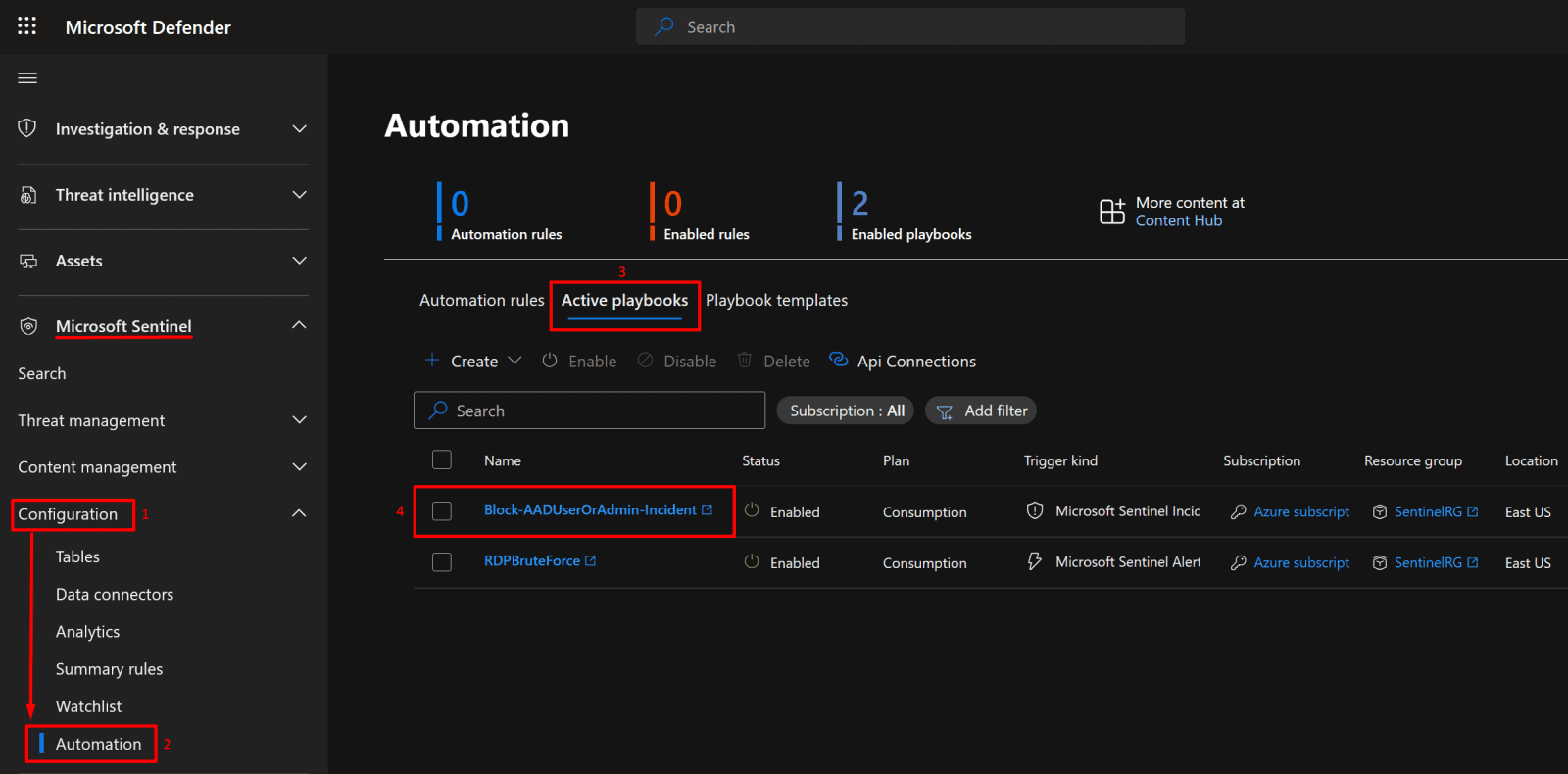
9. Bonus: Use playbook template from Github to block EntraID user.
*
Steps
Create an Azure Sentinel and Logs Analytics workspace.
Azure Sentinel is a cloud-native Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) solution that collects, analyzes, and responds to security events across your environment.
Log Analytics Workspace is the data storage and analysis foundation for Sentinel, it stores logs from connected resources and enables you to run KQL queries for threat detection and investigation.
*
1. In the Azure Portal search bar, type Sentinel and then click Create.

*
2. Create a Logs Analytics workspace for Sentinel.
Note: Sentinel will automatically enable a 31-day free trial for your workspace, allowing you to ingest and analyze data at no cost during this period.

*
3. Fill in the Basics tab:
- Subscription: Select your subscription.
- Resource Group: Choose your resource group (or create a new one).
- Name: Enter a name for your workspace.
- Region: Select your desired region.
Click Review + Create.

*
4. Add Sentinel to a Log Analytics workspace.
- Go to Microsoft Sentinel in the Azure Portal.
- Click on the Log Analytics workspace you created earlier.
- Click Add to enable Microsoft Sentinel for that workspace.


*
Connect the virtual machine to the logs analytics workspace using the AMA connector in the Sentinel portal.
Connect AMA connector in Sentinel portal.
1. Microsoft has moved many Microsoft Sentinel features, like certain connectors or dashboards, into the Microsoft Defender portal.
On the Sentinel page, click on "Click here to go to the Defender portal."

*
Install Windows Security Events via AMA.
2. In Sentinel, go to Content Hub, then search for Windows Security Events via AMA.
- Click "Install."

*
3. Confirm that the package was installed.

*
4. Once installed, the connector becomes available in:
- Microsoft Sentinel → Configuration → Data connectors
- Click on "Open connector page."

*
5. Click on "Create data collection rule" to enter the wizard.
- Give it a name, and then choose your subscription and resource group.
- Click "Next: Resources"

*
6. On resources page choose VM01, then click "Next: Collect"
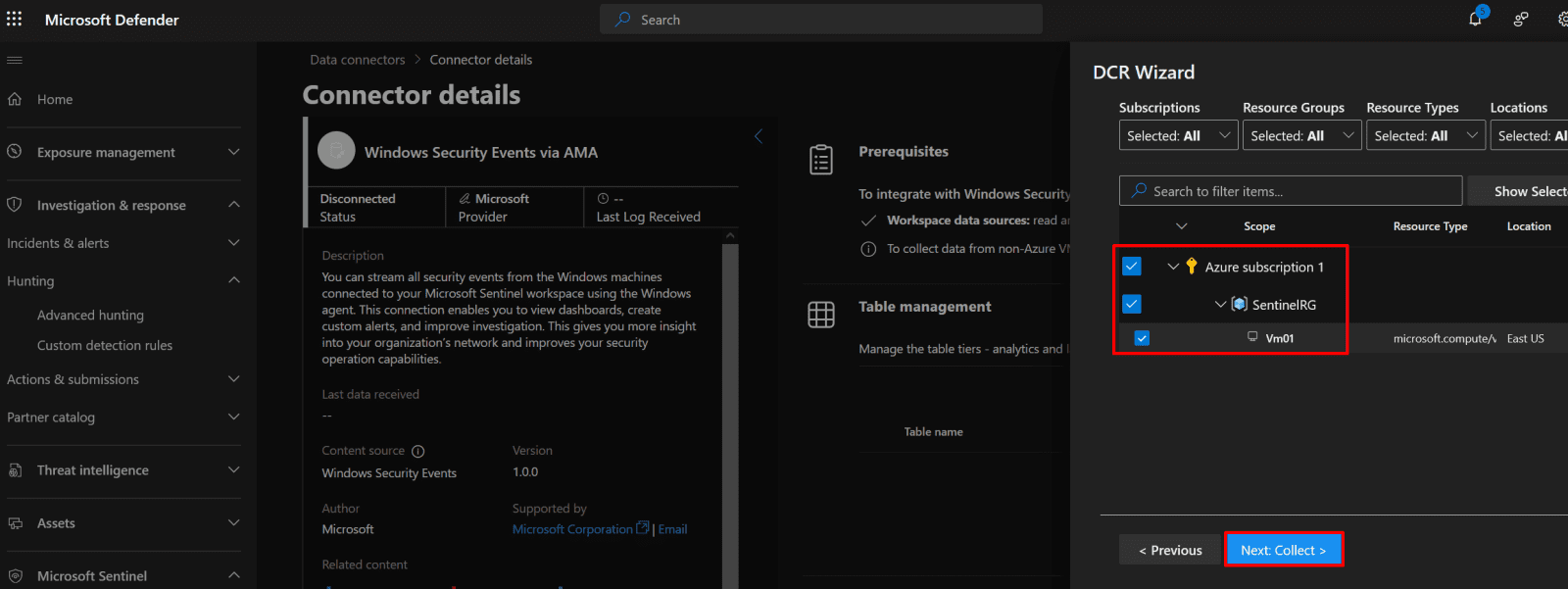
*
7. On the Collect page, select “All Security Events”, then click Next: Review + Create, and finally click Create.
Note: This step creates a Data Collection Rule (DCR) that defines how security events are collected from your virtual machines.