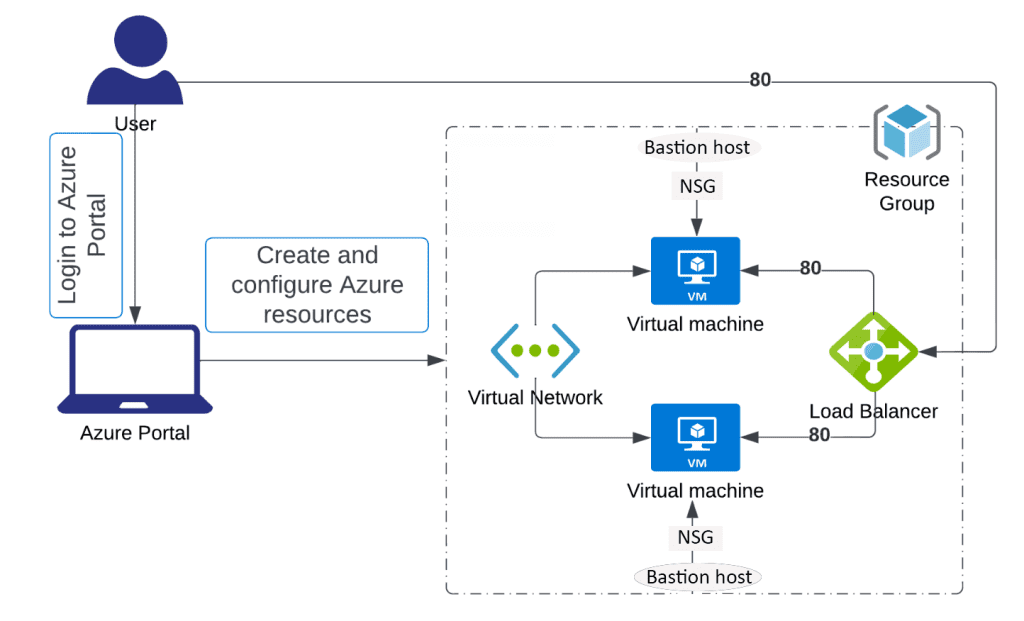
Creating a Secure Standard Public Load Balancer in Azure to Distribute Incoming Network Traffic Across Multiple Virtual Machines.

Task Details
1. Create a Virtual Network
Define the private network space where all your resources will communicate securely.
2. Create Virtual Machines in an Availability Set
Ensure fault tolerance by distributing VMs across multiple fault and update domains.
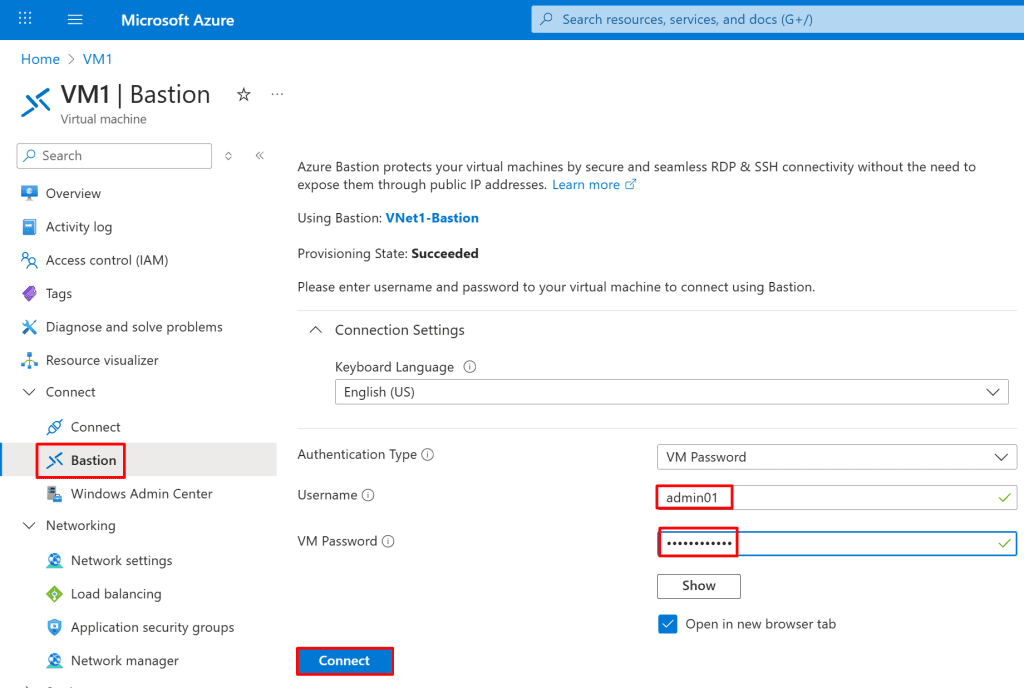
3. Enable Azure Bastion for Secure RDP Access
Connect to your VMs securely via the Azure portal without exposing public IP addresses.
4. Secure the Environment with NSG Rules
Use Network Security Groups to allow only required traffic and block unauthorized access.
Bonus (Optional): Create an NSG for the Subnet and Use ASG-Based Rules
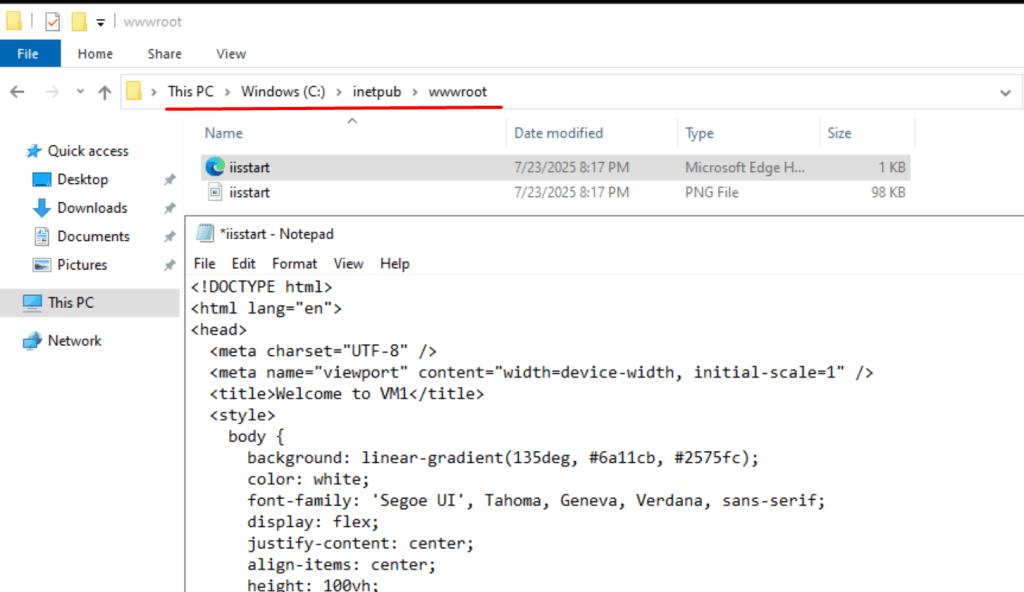
5. Install IIS on Both Virtual Machines with the PowerShell command
Set up the web server role to host your application or test pages.
Bonus: Automate the installation of IIS on all VMs already deployed in the East US region using a PowerShell script.
6. Create a Load Balancer
Distribute incoming traffic evenly across the VMs to ensure high availability and scalability.
7. Test the Load Balancer
Access the frontend IP to verify that traffic is correctly routed to the backend VMs.
Architecture diagram
*
Steps
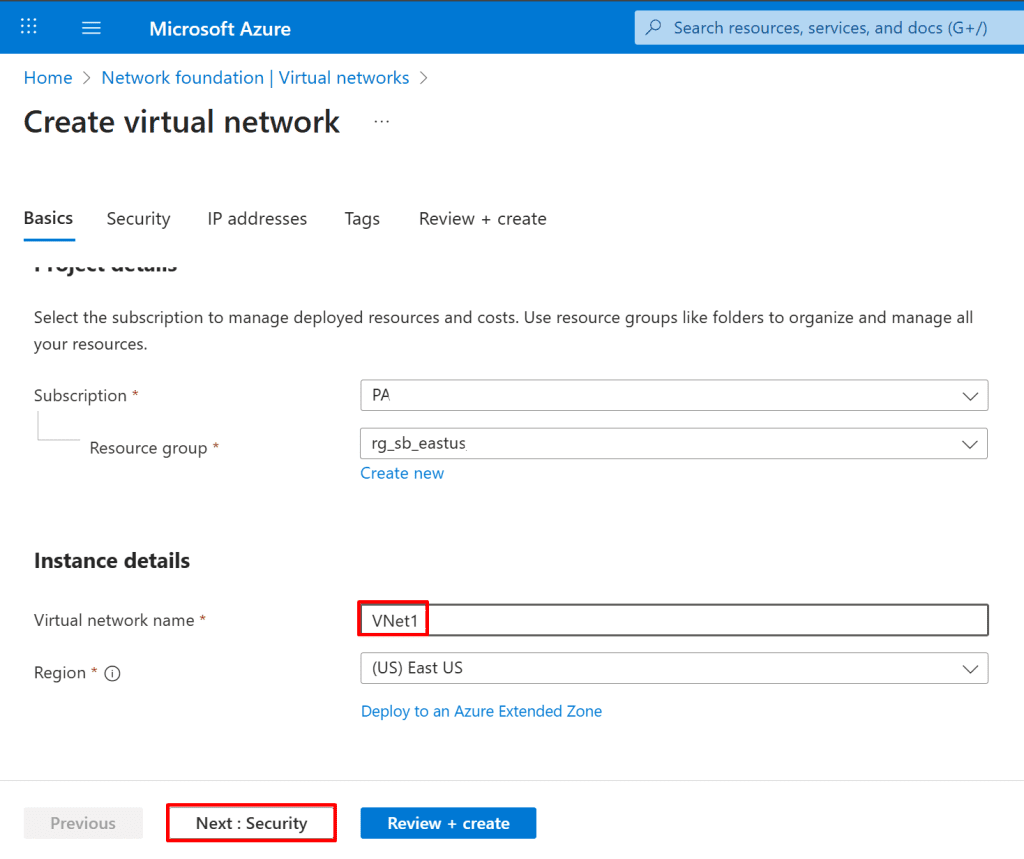
1. Create a virtual network named Vnet1. Within it, define two subnets: one designated for the backend pool and the other for Azure Bastion access.
- In the Azure portal's search bar, type "Virtual networks".
- From the search results under "Services," click "Virtual networks."
- On the Virtual networks page, click the "+ Create" button.

Project details:
- Select your "Subscription" (e.g., PA).
- Choose an existing "Resource group" (e.g., rg_sb_eastus) or click "Create new".
Instance details:
- Enter a "Virtual network name" (e.g., VNet1).
- Select a "Region" (e.g., "(US) East US").
*
2. In the Security tab, enable Azure Bastion and provide a name for the Bastion host. A public IP address will be assigned automatically by default.
Note: You can also choose to create and assign your own public IP address if needed.
Note: The AzureBastionSubnet will be created automatically when you enable Azure Bastion.
Note: You can connect to a VM through Azure Bastion using either the az network bastion rdp command or a native RDP client (mstsc.exe). The CLI command works without needing mstsc.exe, while using mstsc.exe requires Bastion Standard SKU with Native Client Support enabled. All connections remain secure over the VM’s private IP, so no public IP is required.

*
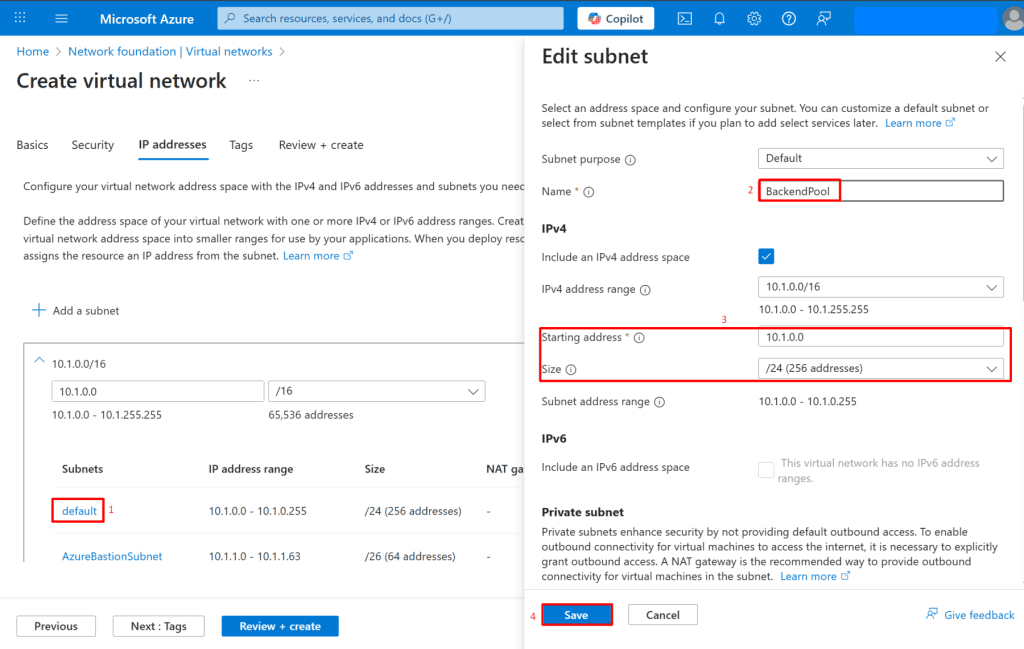
3. Navigate to the IP addresses section and create a new subnet named BackendPool for use with the backend pool of your Load Balancer.
Click on the subnet you wish to edit (e.g., "default"). This will open the "Edit subnet" pane.
Configure Subnet:
- Name: Enter the subnet name (e.g., BackendPool).
- Starting address: Enter the starting IP address for the subnet (e.g., 10.1.0.0).
- Size: Select the subnet size (e.g., /24 (256 addresses)).
- Save: Click the "Save" button to apply changes to the subnet.
Note: A backend pool is a group of virtual machines (VMs) or other resources that receive traffic from a load balancer.
*
4. Create two Virtual Machines.

*
5. On the Basics tab, configure the following:
Resource Group
- Select: Your resource group
Instance Details:
- Virtual Machine Name: VM1
- Region: East US
- Availability Options: Select Availability set
Availability Set:
- Click Create new
- Name: AvailabilitySet
- Fault Domains: 2
- Update Domains: 2
Image:
- Select: Windows Server 2019 Datacenter - Gen2
Azure Spot Instance
- Run with Azure Spot discount: Leave unchecked (default)
Size
- Select: Standard_B2s
Administrator Account
- Username: admin01
- Password: Enter a secure password
- Confirm Password: Re-enter the same password
- Inbound Port Rules
Public Inbound Ports: Select Allow selected ports - Select Inbound Ports: HTTP (80,) RDP (3389)
Note: Using a load balancer with an availability set ensures high availability by distributing VMs across fault and update domains, while using it with standalone VMs offers load distribution but no fault tolerance.
Note:
In this guide, we use an Availability Set to ensure high availability of virtual machines within a single region by distributing them across fault and update domains.
Alternatively, you can use a Virtual Machine Scale Set (VMSS), which provides similar high availability features but also supports automatic scaling and centralized management of a large number of identical VMs.
VMSS is ideal for scenarios requiring elasticity, such as web frontends or stateless applications. If your workload requires dynamic scaling or zone redundancy, consider using VMSS instead of an Availability Set.

*
6. Navigate to the Disks tab and select the appropriate disk type.
*
7. On networking tab
Network Interface Configuration
- Virtual Network: Select VNet1
- Subnet: Select BackendPool
- Public IP: Select None
- Name: Leave the default
- SKU: Select Standard
- Assignment: Select Static
Click OK

*
8. Follow steps 4 to 7 and create another virtual machine and name it VM2
Note: On the Basics tab, under Availability options, select the previously created Availability Set (AvailabilitySet)

*
9. Create a Load Balancer
- On the Load balancers page, click + Create.

In the Basics tab, enter or select the following:
Resource Group Select: Your resource group
Instance Details
- Name: LoadBalancer
- Region: East US
- SKU: Standard
- Type: Public
- Tier: Leave as default: Regional
Note: Basic Load Balancer is being retired on September 30, 2025. If you are currently using it, Microsoft strongly recommends upgrading to Standard Load Balancer.
Note: Azure Basic Load Balancer supports up to 300 instances (VMs or VM scale set instances) in its backend pool.

*
10. Click on Next: Frontend IP configuration, then select + Add a frontend IP configuration.
Note: The Frontend IP Configuration is the public or private IP address and port that the Load Balancer listens on for incoming traffic.
On the Add IP configuration page, enter or select the following:
- Name: Enter myFrontend
- IP version: Leave the default IPv4
Public IP address: Click Create new
- Name: Enter LB-PublicIP
- Assignment: Static
Click save and next: Backend pools

*
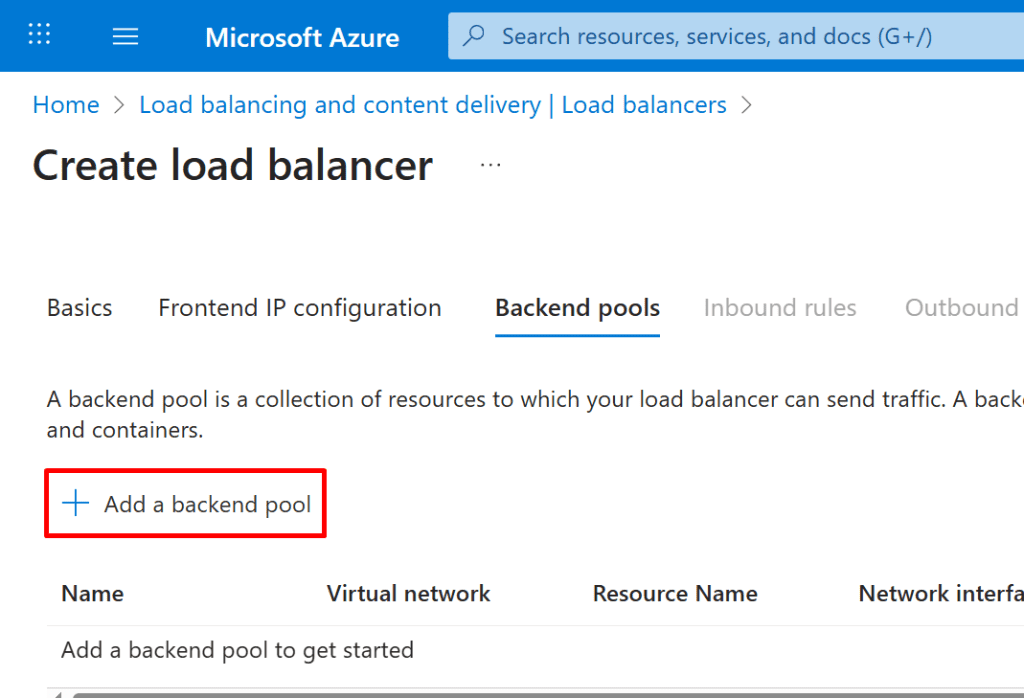
11. On the Backend pools page, click + Add a backend pool.